
Protecting Sensitive Data in the Cloud: A Small Business Guide
A cloud storage misconfiguration was responsible for exposing the personal data of 97% of Americans. Learn how to keep your business’s cloud systems safe in this comprehensive guide.

A cloud storage misconfiguration was responsible for exposing the personal data of 97% of Americans. Learn how to keep your business’s cloud systems safe in this comprehensive guide.

Cyber threat hunting is a proactive approach to cybersecurity that involves actively searching for hidden threats within an organization’s networks and systems. By proactively seeking out threats, small businesses can reduce their risk of falling victim to cyberattacks, data breaches, and other security incidents.
Phishing, smishing, vishing, and whaling are serious threats to businesses of all sizes, with attackers constantly finding new ways to exploit vulnerabilities. By educating employees, implementing technical solutions, and working with cybersecurity experts, organizations can significantly reduce the risk of falling victim to these dangerous cyber attacks.

Nearly 50% of companies now have cyber insurance policies, up from just 34% two years ago, reflecting the growing recognition among businesses that cyber incidents pose a severe threat to their operations and financial stability. As cyber threats evolve, companies must continuously assess their unique risk profile to determine if they would benefit from a standalone cyber insurance policy.

Businesses must implement robust security measures to protect their data and comply with evolving compliance requirements, especially small and medium-sized businesses without dedicated cybersecurity resources. This guide helps SMB executives navigate endpoint security compliance, understand key requirements, and adopt best practices to safeguard their organization and maintain compliance in a challenging cybersecurity environment.

Endpoint Detection and Response (EDR) and Managed Detection and Response (MDR) are advanced solutions that provide better visibility, threat detection, and response capabilities for small and medium businesses facing cyber threats. Integrating EDR/MDR with firewalls, Security Information and Event Management (SIEM), Identity and Access Management (IAM), and email security can significantly strengthen your cyber defenses.

Endpoint Detection and Response (EDR) and Managed Detection and Response (MDR) have emerged to address the shortcomings of antivirus and provide comprehensive endpoint protection, offering advanced capabilities such as behavioral analysis, threat hunting, and automated response actions to detect and respond to threats that evade traditional antivirus.

MDR is a powerful solution that can help organizations improve their security posture and protect their endpoints from advanced cyber threats. By providing 24/7 monitoring, threat hunting, and incident response capabilities, MDR can significantly reduce the risk of data breaches and other security incidents.

Structured data backups are crucial in protecting your business from ransomware and other threats. By implementing segregated backups and regular testing, you can ensure your data is secure and recoverable in case of an attack.
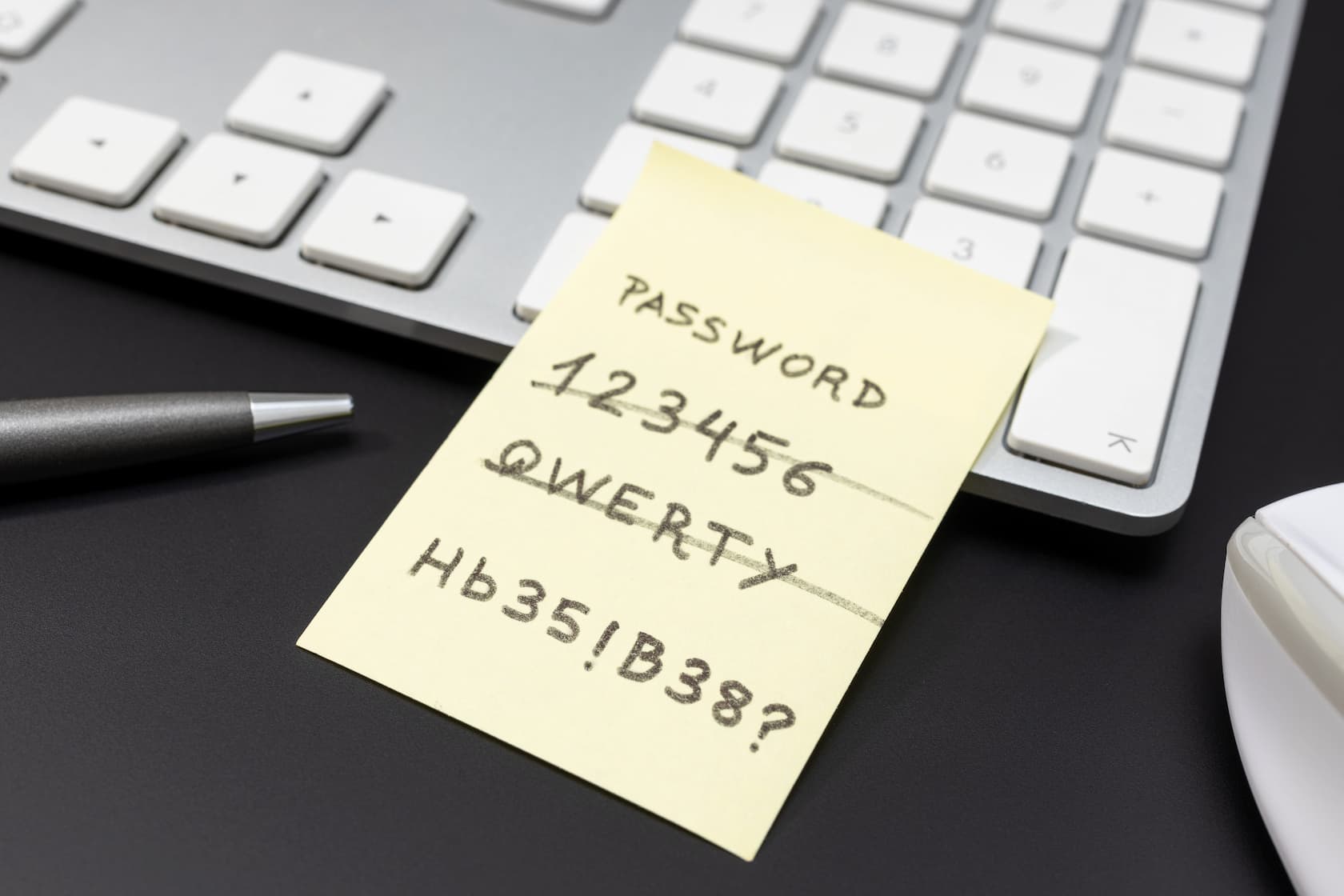
Small-to-medium businesses in 2023 used an average of 253 Software as a Service (SaaS) products, leading to over ten thousand unique accounts that require passwords. Password managers offer a solution to securely store, generate, and manage passwords, reducing the risk of cybersecurity breaches for businesses.
Hear from us once a month with product updates and company news.